Description
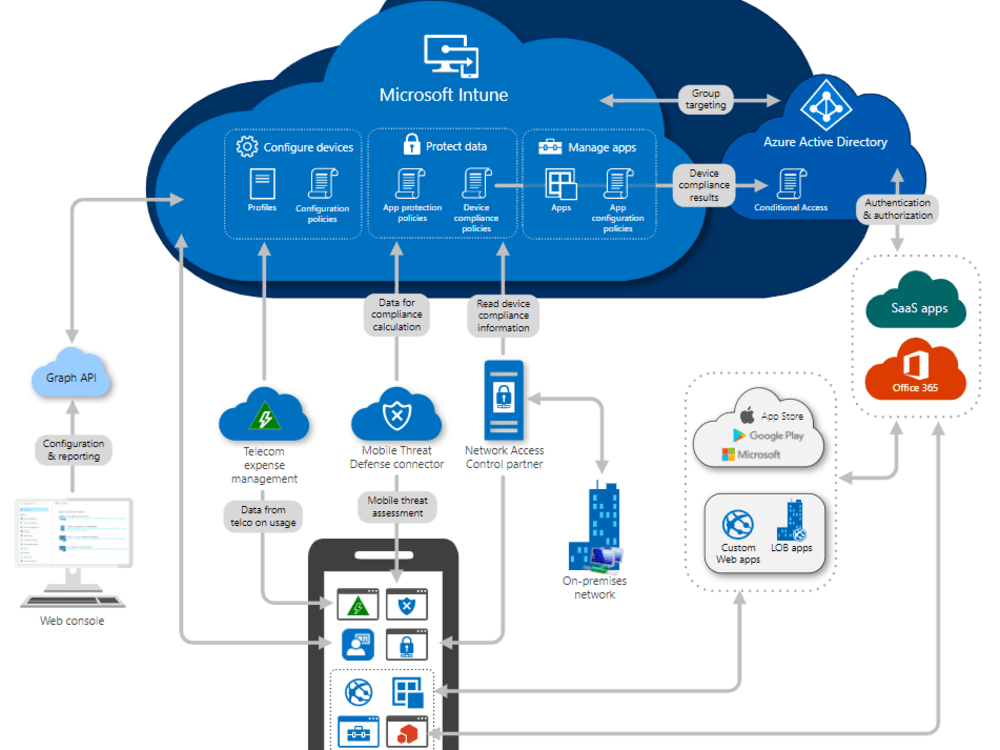
Firewall Configuration & Monitoring protects your digital assets by controlling and monitoring traffic entering or leaving your network. We begin with assessing your infrastructure to define optimal firewall rules, minimizing the attack surface without impacting business operations. Once deployed, we continuously monitor firewall logs, look for intrusion attempts, and update configurations as needed. Our service covers both physical and virtual firewalls, and supports leading platforms like Cisco, Fortinet, Palo Alto, and cloud-native solutions. We provide detailed reports on attempted breaches and recommendations for additional layers of defense. By ensuring your firewall is always aligned with your security policies and evolving threats, we keep your network secure, compliant, and high-performing.


Nana –
Firewall Configuration & Monitoring provides a robust service, ensuring network security through meticulous configuration and proactive monitoring. Their responsiveness to potential threats and clear communication makes them a reliable partner in safeguarding our critical infrastructure.
Abdullahi –
Firewall Configuration & Monitoring provided a robust security posture. Their setup was thorough, addressing key vulnerabilities. We appreciated the real-time monitoring and proactive threat detection, which significantly improved our network security. Their support team was responsive and knowledgeable.
Godspower –
Firewall Configuration & Monitoring provides a solid service with timely configuration updates and attentive monitoring. Their team demonstrates a good understanding of security protocols. Their proactive approach ensures network security posture is maintained. A reliable choice for businesses seeking robust protection.
Kenneth –
Firewall Configuration & Monitoring provides robust security measures. They offer efficient setup and vigilant monitoring of firewalls, protecting networks from potential threats. Their expertise in firewall management ensures peace of mind and allows businesses to focus on core operations. They are a reliable partner for data protection.